We’ve moved well beyond the simple password and PIN for security of our electronic devices. And nowhere does that hold as true as when it comes to your phone.
Sure, every smartphone comes with the option to set a password or PIN to access its contents. And apps, like those for mobile payments or work-related documents, can further be protected with another layer of passwords/PINs. But simple protection can go well beyond that.
Here are a few additional ways that you can protect data on your smartphone
 1.Biometric fingerprint scanner
1.Biometric fingerprint scanner
It’s becoming more and more common to find a biometric fingerprint sensor in a mobile phone, allowing the owner to store his thumbprint for quick and easy access to the device, as well as downloading apps without having to re-enter an iTunes password every time. The Home button on all new iPhones, for example, can be used as a fingerprint sensor through Touch ID. This adds another layer of security should you choose to use it. And unlike a PIN or password, a thumbprint can’t be duplicated or spoofed – at least not nearly as easily.
 2.Knock Codes
2.Knock Codes
Devices like the LG G4 include a neat Knock Code option that lets you draw a patterned passcode versus using basic alphanumeric options. So instead of making your passcode “36547,” for example, you can knock up to eight times in four quadrants of the phone’s screen to set an unlock code. It allows for 86,000 possible combinations, and makes it that much more difficult for others to get into your phone. Without a keypad popping up for them to enter numbers, they’d have no idea what to do to unlock the device.
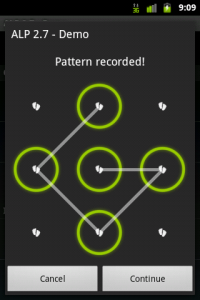 3.Pattern Codes
3.Pattern Codes
Similar to the knock method, many Android phones have pattern locks, which let you slide your finger along the screen in a personalized pattern in order to lock the device. You could, for example, draw the outline of a square followed by a diagonal line from the top right to bottom left corner as your unique unlock code. Keep in mind, however, that if you run a Google search for pattern codes, you’ll find the most common result pertains to how to unlock a device once you’ve forgotten yours! So try not to be too complex, and use a pattern that’s relatively easy for you to remember. And always use a pattern code as only one layer of security – judging from the search results, there are a number of ways one can bypass this security method.
 4.Secret files or folders
4.Secret files or folders
Some phones contain a separate compartment, so to speak, where you can store business-related or other sensitive data separately. This way, you can comfortably hand your device to a friend or family member who wants to scroll through your latest vacation photos without worrying that they might come across a confidential business document or private conversations. In Samsung devices, this secure area is provided by the Knox security solution, which lets the user press a button to switch from Personal use to Work use, hiding files, folders, apps, and other detail when they’re off hours, then bringing them back to the forefront once the work day begins. It’s an ideal solution for those who follow the Bring Your Own Device (BYOD) strategy in the office.
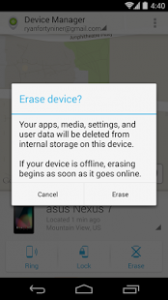 5.Remote wiping
5.Remote wiping
Though it’s the most extreme method of protecting data on your phone, many devices nowadays include the capability for remote wiping, allowing you to use another device, like your computer, to wipe the phone of its content should it become lost or stolen. With many Android devices, for example, you can use the Android Device Manager tracking tool to log into your device from a Google account on a computer, and select “remote lock and erase,” as long as the feature is enabled on your phone. As a first defense, many devices will let you first just remotely lock the phone so a thief can’t get into it at all. But if you feel that the data is far too sensitive to risk, remote wiping is a great security measure in addition to all of those noted above. (Just make sure you have the data backed up somewhere.) It’s a great insurance policy allowing you to confidently store information on your phone and ensure it won’t get into the wrong hands.



