The Canadian Radio-television and Telecommunications Commission (CRTC) has its hands full with all things Internet these days, not the least of which is looking at the country-wide network outage at Rogers on July 8 that prevented many Canadians from getting online.
But just a week or so prior to that, the CRTC made a major ruling that affects all Internet Service Providers (ISPs) in the country, not just Rogers: it has decided they will have to block botnets and associated websites that are under the control of a server operated by a malicious actor.
(Botnets are networks of malware-infected computers, or bots, that can automatically enable spam, distributed denial-of-service attacks, malware deployment and even information theft – they can also be used to give hackers free access to other networks.)
And while malicious botnet activity is said by the CRTC to be significant, the blocking may not start for months, until a mechanism at the network level has been worked out.
Until then, with more than half of us spending more than a quarter of our time online, surfing the Web can be risky business, especially if bumping into the wrong site leads to the infection of a personal laptop or an entire network.
The CRTC did suggest that a framework to block botnets could include a centrally managed list of identified malicious Internet addresses, one overseen by an agency such as the federal government’s Canadian Centre for Cyber Security, the Canadian Internet Registry Authority (CIRA), or even a new independent agency. Such lists can be and are regularly updated, even daily.
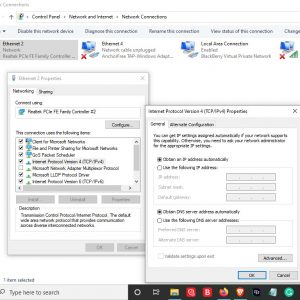 CIRA, the group that oversees the .ca Internet domain, already does have a botnet blocking tool called Canadian Shield. It acts as an added layer of protection for those diligent and vigilant enough to install it: it does require the computer end user to add a configuration file to their router for protection, a step many are not familiar or comfortable with, so the pick-up rate for the Canadian blocker was slower in the beginning (but eventually, some four million Canadians made use of the service, CIRA reports). Mobile versions are available in the Apple App Store and Google Play Store.
CIRA, the group that oversees the .ca Internet domain, already does have a botnet blocking tool called Canadian Shield. It acts as an added layer of protection for those diligent and vigilant enough to install it: it does require the computer end user to add a configuration file to their router for protection, a step many are not familiar or comfortable with, so the pick-up rate for the Canadian blocker was slower in the beginning (but eventually, some four million Canadians made use of the service, CIRA reports). Mobile versions are available in the Apple App Store and Google Play Store.
In 2021, CIRA announced a partnership with ScamAdviser, a global anti-scam technology company, to integrate added protection against fraudulent websites into its 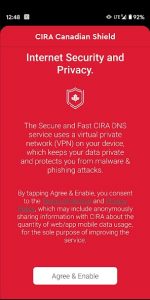 Canadian Shield.
Canadian Shield.
More recently, CIRA launched a desktop browser extension for Canadian Shield designed to make it easier for Canadians to protect against online threats like harmful malware, phishing attempts, scams and other malicious actors. The free-to-use extension is available for browsers like Google Chrome and Mozilla Firefox with other compatibilities said to be coming soon.
Through its partnership with Mozilla, the organization behind Firefox, Canadian Shield works automatically with that browser to stop visitors from going to malicious websites. Since it was made the default DNS over HTTPS provider for Firefox users in Canada last summer, CIRA has become the first organization to provide country-specific encrypted DNS services with Mozilla.
(A DNS, or domain name server, is like a directory, or a phone book, for the Internet. We type a recognizable website name; the directory converts and links that name to a numerical IP address of the server where the website we want to visit is hosted. But by disguising their malicious IP addresses as a legitimate company website address, often with slight misspellings or very similar names, malicious actors can hijack the supposed safe visit. DNS is used in more than 90 per cent of all malware and phishing attacks; malicious DNS entries are known, identified and blocked whenever possible using tools like the Canadian Shield.)
“This browser extension continues CIRA’s momentum of building a safer internet for Canadians by making it simple and easy for anyone, no matter their level of knowledge, to protect themselves online. We keep users’ data private and enhance online security,” Tanya O’Callaghan, Vice President, Community Investment, Policy and Advocacy at CIRA said when the extension was unveiled.
Keeping users’ data private is important at CIRA, which is an independent non-profit organization, not really a government agency. It cites with satisfaction that its privacy policy was recently audited.
Likewise, CIRA touts the fact that with data centres in Toronto, Vancouver and Montreal, personal data stays in Canada rather than being possibly stored on servers outside the country, a potential risk to the privacy and security of personal information.
Software developers and issue response team members are also in Canada, and the organization has shown it can respond to issues or safety concerns with its service: an independent security researcher identified a vulnerability in the Canadian Shield (and how it applied validation certificates in older iOS versions): he communicated his findings to CIRA, and, within weeks, an updated version was released with a fix for the problem.
# # #

Last year, CIRA reports, its Canadian Shield blocked more than 36 million requests to malicious domains. Image courtesy CIRA.
-30-